Tag: TECHNICAL
While CRQCs capable of breaking current public key encryption algorithms have not yet materialized, technological advancements are pushing us towards what is ominously dubbed 'Q-Day'—the day a CRQC becomes operational. Many experts believe that Q-Day, or Y2Q as it's sometimes called, is just around the corner, suggesting it could occur by 2030 or even sooner; some speculate it may already exist within secret government laboratories.
Fidelity in quantum computing measures the accuracy of quantum operations, including how effectively a quantum computer can perform calculations without errors. In quantum systems, noise and decoherence can degrade the coherence of quantum states, leading to errors and reduced computational accuracy. Errors are not just common; they're expected. Quantum states are delicate, easily disturbed by external factors like temperature fluctuations, electromagnetic fields, and even stray cosmic rays.
"Harvest Now, Decrypt Later" (HNDL), also known as "Store Now, Decrypt Later" (SNDL), is a concerning risk where adversaries collect encrypted data with the intent to decrypt it once quantum computing becomes capable of breaking current encryption methods. This is the quantum computing's ticking time bomb, with potential implications for every encrypted byte of data currently considered secure.
The transition to post-quantum cryptography is a complex, multi-faceted process that requires careful planning, significant investment, and a proactive, adaptable approach. By addressing these challenges head-on and preparing for the dynamic cryptographic landscape of the future, organizations can achieve crypto-agility and secure their digital assets against the emerging quantum threat.
In my work with various clients, I frequently encounter a significant misunderstanding about the scope of preparations required to become quantum ready. Many assume that the transition to a post-quantum world will be straightforward, involving only minor patches to a few systems or simple upgrades to hardware security modules (HSMs). Unfortunately, this is a dangerous misconception. Preparing for this seismic shift is far more complex than most realize.
As we edge closer to the Q-Day—the anticipated moment when quantum computers will be capable of breaking traditional cryptographic systems—the need for crypto-agility becomes increasingly critical. Crypto-agility is the capability of an organization to swiftly and efficiently transition between different cryptographic algorithms and protocols in response to emerging threats and technological advancements.
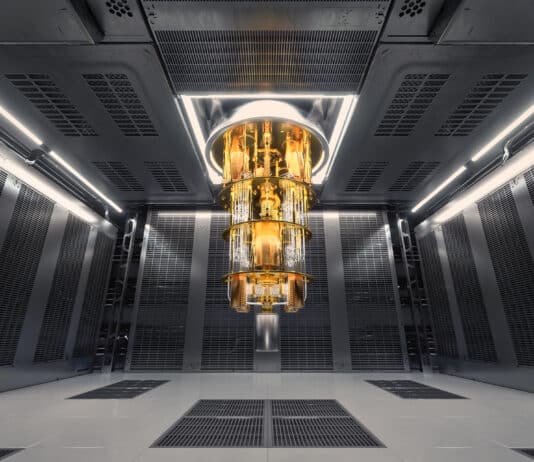
As quantum technologies garner global attention, its economic and national security implications are positioning these set of technologies alongside AI and 5G as pivotal emerging technologies for the future. Governments worldwide are recognizing the strategic importance of quantum technologies, which broadly includes quantum computing, quantum communication and quantum sensing.
The journey towards quantum resistance is not merely about staying ahead of a theoretical threat but about evolving our cybersecurity practices in line with technological advancements. Starting preparations now ensures that organizations are not caught off guard when the landscape shifts. It’s about being informed, vigilant, and proactive—qualities essential to navigating any future technological shifts.
As the quantum era approaches, organizations face the daunting task of protecting their sensitive data from the looming threat of quantum computers. These powerful machines have the potential to render traditional cryptographic methods obsolete, making it imperative to explore innovative strategies for quantum readiness. One often overlooked yet highly promising approach is tokenization.
Adiabatic Quantum Computing (AQC), and its variant Quantum Annealing, are another model for quantum computation. It's a specialized subset of quantum computing focused on solving optimization problems by finding the minimum (or maximum) of a given function over a set of possible solutions. For problems that can be presented as optimization problems, such as 3-SAT problem, quantum database search problem, and yes, the factoring problem we are worried about, quantum annealers have shown great potential in solving them in a way that classical computers struggle with.
The 5G Core network is a Service Based Architecture. It evolves the traditional appliance based 4G Core Network to support services. It offers more...
The telecoms and digital technologies sectors are notoriously jargonised. Eavesdrop on any conversation at an industry conference (remember those?) and you’d be treated to...
It's been a year of contradictions for the telecommunications industry.
Like most sectors, it has been heavily impacted by the consequences of the Covid-19 pandemic,...
In the recent report by IHS Markit - "The 5G Economy - How 5G will contribute to the global economy" - researchers claimed that...
Neil Harbisson calls himself a cyborg. Without the antenna implanted in his skull, he would not be able to see colour of any kind....