Tag: TECHNICAL
The interest in 5G and mIoT is exploding. It's exciting to see so many IT and cybersecurity professionals in my network trying to learn...
In a recent session on smart building cybersecurity, a student cheekily asked me "How did we ever connect anything before 5G?" At that moment...
In a major milestone for 5G, 3GPP finalized the Release 16 in July - its second set of specifications for 5G New Radio (NR)...
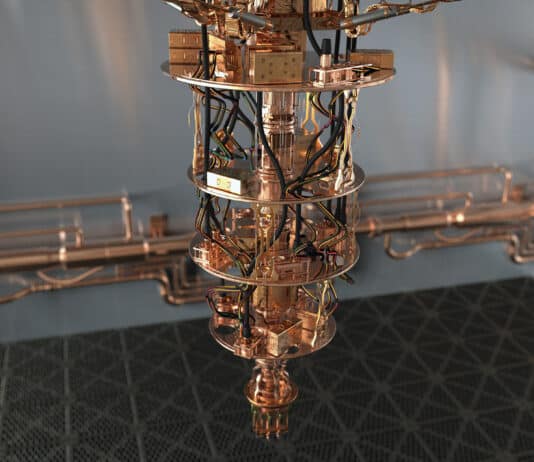
Since the early 2000s, the field of quantum computing has seen significant advancements, both in technological development and in commercialization efforts. The experimental demonstration of Shor's algorithm in 2001 proved to be one of the key catalyzing events, spurring increased interest and investment from both the public and private sectors.
No, no it doesn’t. Huawei's code might as well be extremely secure. Their code is certainly the most scrutinized. But the recent UDG source...
IoT Wireless Protocols data rate and range comparison in a spreadsheet format. Includes downloadable Excel spreadsheet.
IoT Wireless Protocols in a spreadsheet format. Includes downloadable Excel spreadsheet.
Quantum Key Distribution (QKD) represents a radical advancement in secure communication, utilizing principles from quantum mechanics to distribute cryptographic keys with guaranteed security.Unlike classical encryption, whose security often relies on the computational difficulty of certain mathematical problems, QKD's security is based on the laws of physics, which are, as far as we know, unbreakable.
Depending on who you speak to, 5G is either humankind’s greatest imminent blessing or its greatest imminent curse. Still in its infancy, and not...
The secret sauce of quantum computing, which even Einstein called "spooky," is the ability to generate and manipulate quantum bits of data or qubits. Certain computational tasks can be executed exponentially faster on a quantum processor using qubits, than on a classical computer with 1s and 0s. A qubit can attain a third state of superimposition of 1s and 0s simultaneously, encode data into quantum mechanical properties by "entangling" pairs of qubits, manipulate that data and perform huge complex calculations very quickly.
NFC is a short range two-way wireless communication technology that enables simple and secure communication between electronic devices embedded with NFC microchip. NFC technology...
Radio-Frequency Identification (RFID) is a technology commonly used for identification, status administration and management of different objects. It is important for people identification, as it...
If you've ever been to an expensive restaurant and ordered a familiar dish like, say, lasagna, but received a plate with five different elements...
The Wi-Fi represents wireless technology that includes the IEEE 802.11 family of standards (IEEE 802.11a, IEEE 802.11b, IEEE 802.11g, IEEE 802.11n, IEEE 802.11ac, etc.)....
Bluetooth is short-range wireless communications technology based on the IEEE 802.15.1 protocol. It works in a crowded license free 2.4 GHz frequency band and...